Tresorit is another cloud storage provider similar to Dropbox, SpiderOak, Google Drive, or Box. Much like SpiderOak, Tresorit seems to value security and privacy above all else. However, unlike SpiderOak, whose user-interface can feel old and unintuitive, Tresorit does a good job keeping the design and user-interactions simple and modern.
Tresorit is another cloud storage provider similar to Dropbox, SpiderOak, Google Drive, or Box. Much like SpiderOak, Tresorit seems to value security and privacy above all else. However, unlike SpiderOak, whose user-interface can feel old and unintuitive, Tresorit does a good job keeping the design and user-interactions simple and modern.
Tresorit is free for up to 5GB with the option of gaining up to 16GB for free through referrals. The paid options start at 20GB for $8 per month.
Pros & Cons
Pros
- Excellent security
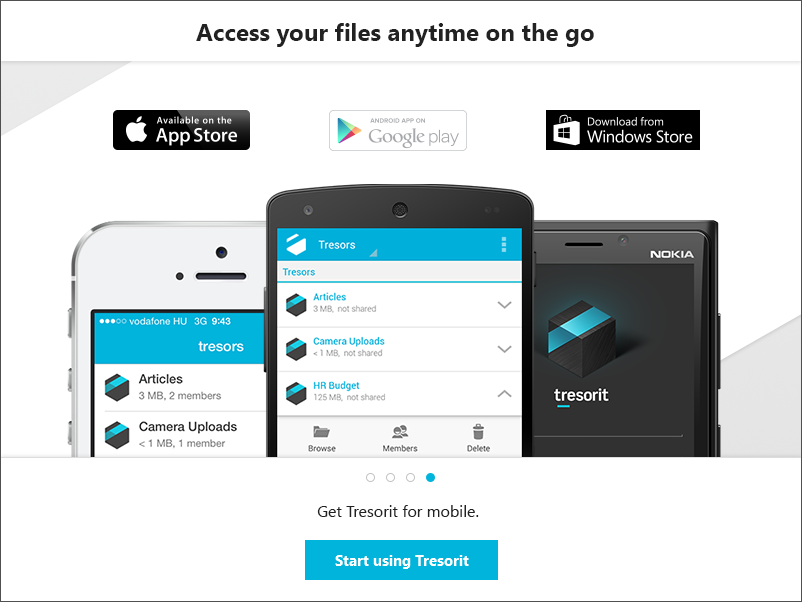
- Apps available for all major platforms
- Modern design
- Easy to create encrypted folders
- Easy to share encrypted files or folders
Cons
- Deleted files are gone forever
- Sharing files increases security risk
- Only 5GB free. Pricing is higher per gigabyte than some competitors
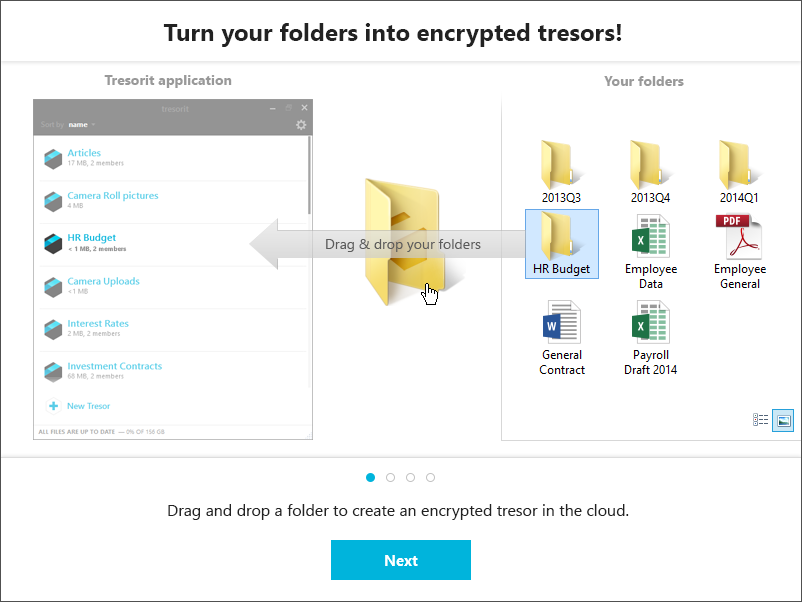
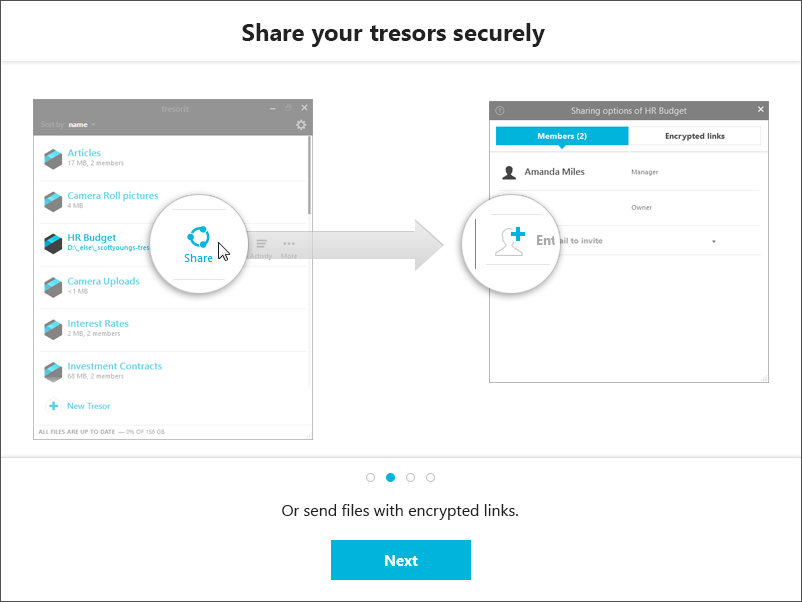
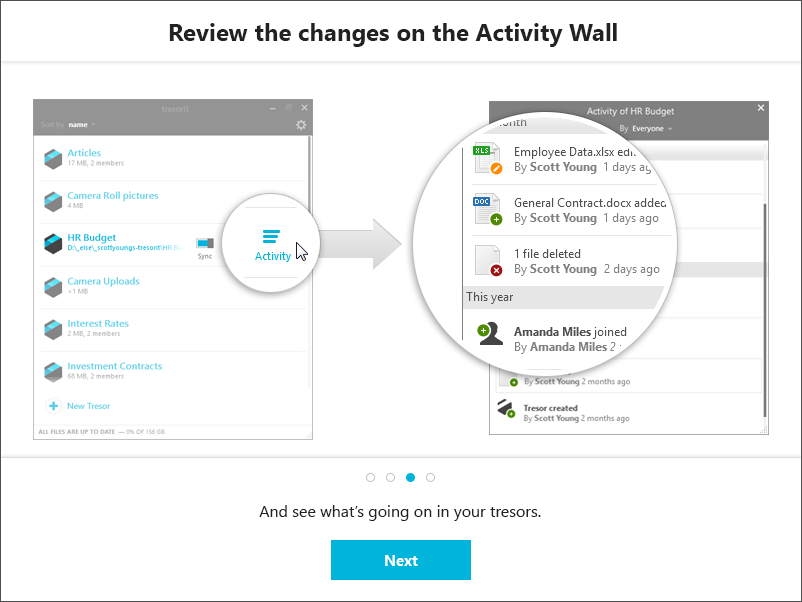
When first installing Tresorit, you are greeted by this quick introduction demonstrating how Tresorit works. I have taken screenshots of the introduction and put them in a image gallery below:
Design and Usability
The design of the Tresorit application is clean and modern. After logging in for the first time there is a window that shows all your “tresors” and their sync status. From this window you can turn syncing on/off, begin sharing a folder, and view recent activity for that folder such as when it has been accessed, synced, or edited. In case you are wondering, “tresor” is the German word for “safe” or “vault.”
To add a new tresor you simply click on the + button to create a new synced folder (a “tresor”) or drag any file or folder into the main Tresorit window. You can also add files or folders to be backed up and synced by simply right-clicking on the item and using the context menu. If you prefer an experience more like Dropbox, you can easily create a single folder and then move anything you want backed up and synced into that primary Tresorit folder.

There are some issues with Tresorit. Although a versioning system is in place, if a file is deleted locally, it is automatically deleted in the cloud without a way to recover it. This can be problematic if you are using Tresorit for backing up files and accidentally delete something important. Most other cloud storage providers have methods to recover deleted files. This is something we think is important for any cloud service, and hope Tresorit’s versioning system includes deleted files soon.
Security
Security is Tresorit’s most important feature and it is heavily marketed. They even held a contest for hackers to break their client-side encryption for a bounty of $50,000 which has not been claimed. Like SpiderOak, Tresorit does the encryption on your device prior to anything being uploaded. That means they do not have your password or encryption keys and therefore cannot read your data. Even if a hacker was able to access their servers they would have to decrypt the data before it was readable and to do that they would have to brute-force break each individual’s encryption keys. On the other hand, it also means that they do not know your password and it cannot be recovered if you forget it – if you cannot remember your password your data that is stored in the cloud will essentially be lost.
Tresort uses AES 256 in addition to a proprietary encryption algorithm on top of that. How does this compare to SpiderOak? I did a brief review of SpiderOak some time ago and at that time they were definitely the most secure cloud storage provider. SpiderOak is about as secure as Tresorit, but one issue bought up by the heartbleed fiasco is SpiderOak’s option of viewing and downloading files from the cloud using a standard web interface. As we all know after heartbleed, standard web interface cryptographic methods can be exploited. To give SpiderOak credit, you do not have to sign in using their web interface and they encourage you not to, but if you do, you are viewing those documents in a much less secure fashion. It is possible to login to Tresorit on the web via the installed app, to view your account information, but no files or folders are visible.
Sharing your files is an option in both SpiderOak and Tresorit and is likely fairly secure. However, an academic paper from Johns Hopkins University earlier this year looked at the various “zero-knowledge” cloud storage providers like Tresorit and SpiderOak and found that they could all technically decrypt shared data if they wanted to because they are acting as the certificate authority in addition to hosting the data. The obvious solution to this is, do not share anything unless you do not mind others seeing it!
However, both SpiderOak and Tresorit have said that the Johns Hopkins paper is flawed. SpiderOak publicly challenged the paper on their blog, and Tresorit has told me that they also found some issues with the authors’ methodology and conclusions. I was able to ask the Tresorit cryptography team their thoughts regarding the John Hopkins’ study. They confirmed that theoretically “the overall conclusion of the report is valid – there is a certain degree of trust that collaborating with Tresorit requires.” However, they suggested that “the scope of the trust and potential vulnerabilities are much less significant than the report makes them out to be because the researchers misunderstood some of the workings of the service based on their analysis of our code.”
The researchers hypothesize that Tresorit has a way of gaining access to your stored (and encrypted) data through the threat model they propose. However, the model only works for data that is actually in the process of being shared with someone else. Tresorit technologically has NO way of accessing the private key that is used to encrypt everything you store and sync with the service.
The attack model would only be possible if Tresorit was acting maliciously, or had been breached, and even then, would only be limited to a certain, targeted user, not all Tresorit users. Assuming that happened, the attacker would only have access to any data that the user shared AFTER the breach occurred. The user’s, unshared, private data uploaded before or after the breach would still be secure.
The alternatives they propose don’t remove this modicum of trust from the operation, they just shift the trust from the cloud provider to a certificate authority. Unfortunately, certificate authorities are high-profile targets for attackers, as they are crucial for internet trust and security. This is part of the reason why we decided that Tresorit can only ultimately trust itself, and designed our privacy protecting sharing accordingly.
Performance
In my testing Tresorit has performed well. There is no noticeable lag between adding folders or documents and them getting uploaded and synced to my other devices. Upload speeds seem to be essentially capped at my ISPs upload limit. Syncing large files to other computers was fairly fast, but was not limited by my ISPs download cap.
Conclusion
Tresorit is an excellent backup and syncing tool for those who are concerned with security and privacy. If you need to store important personal or business documents in the cloud, Tresorit is probably one of the best option right now.
If you found this review helpful, please let me know by sharing it or by clicking the 1+ button below. If you have any questions, please ask them in the comments section.
| Review Summary | |
|---|---|
| Product: | Tresorit |
| Description: | Tresorit is a secure cloud storage solution that is easy to use. |
| Rating: | 8.0 out of 10. |
| Author: | Cam Medlin |
| Editor: | R.G. Medlin |
| Published: | |
| Updated: | |